You open your inbox one morning and find three messages from friends asking why you sent them a strange link. You didn’t send anything. Your inbox looks completely normal. Nothing seems obviously wrong, but something feels off.
That moment of confusion is how most people first find out their email has been compromised. Not through a dramatic alert or an obvious warning, but through something small that doesn’t quite add up.
Here’s how to know for sure, and exactly what to do about it.
The Warning Signs You Should Not Ignore
Most people miss the early signs because they look minor. A login notification here, a missing email there. By the time something obvious happens, a hacker has often already been inside for days.
Your contacts are receiving emails you never sent
This is the most common sign and the one people notice first, usually because a friend texts them directly. Hackers use your account to send phishing links or scam messages to your contact list because people trust emails from someone they already know. Check your Sent folder right now. If you find emails you didn’t write, that’s your answer. Skilled hackers often delete sent messages to cover their tracks, so an unusually empty Sent folder is itself a red flag worth investigating.
Password reset emails are arriving out of nowhere
This one is serious and easy to misread as spam. When someone has access to your email, they use it to trigger password resets on your other accounts, like your bank, social media, and shopping profiles. They don’t need to know those passwords. They just need your inbox to complete the reset. If you’re getting reset emails you didn’t request, someone is likely already inside.
Login alerts from locations you don’t recognise
Gmail, Outlook, and Yahoo all show recent login activity, including device type and approximate location. Go check yours right now. A login from a country you’ve never visited, or from a device you don’t own, is about as clear a sign as it gets. Some hackers won’t lock you out immediately. Instead, they stay hidden, monitoring your emails quietly for days or weeks while setting things up.
Your account settings have changed without you touching them
This one catches people completely off guard. Hackers often set up automatic forwarding rules that send copies of all your incoming emails to another address. Your emails still arrive normally in your inbox, so nothing looks wrong from your end. But every message you receive is being silently forwarded elsewhere. Check your email settings for any forwarding rules or inbox filters you didn’t create and delete anything unfamiliar immediately.
Your correct password suddenly stops working
When a hacker gets in, they sometimes change your password, your two-factor authentication settings, and your recovery options all at once. This makes the standard account recovery process much harder. If you’re certain you’re typing the right password and it’s not working, don’t assume you forgot it. Treat it as a compromise until proven otherwise.
One Quick Check Before You Do Anything Else
Go to haveibeenpwned.com and type in your email address. The site checks it against a database of known data breaches and tells you immediately if your credentials were exposed. It’s free and takes about ten seconds.
If your email shows up in a breach, that explains how they got in. Hackers routinely buy leaked credential lists from the dark web and run automated scripts that try those usernames and passwords across Gmail, Outlook, Yahoo, and other popular providers. If you’ve ever reused the same password across multiple sites, that’s the gap they walked through.
This check doesn’t replace the steps below. But it tells you whether you’re dealing with a targeted attack or a bulk automated attempt, and that context matters for how urgently you need to act.
What to Do Right Now, In This Order
Don’t skip steps here. The sequence matters more than speed.
Step 1: Change your password immediately
\Use a device you personally own and a network you trust, not a public computer or shared Wi-Fi. Create a completely new password, at least 15 characters, mixing letters, numbers, and symbols. Don’t recycle an old one from any other account.
Step 2: Turn on two-factor authentication
This is the single most effective thing you can do right now. Even if someone has your new password, they can’t get in without the second verification step. Use an authenticator app like Google Authenticator or Authy rather than SMS codes. SMS can be intercepted. Authenticator apps cannot.
Step 3: Remove any forwarding rules you didn’t create
Go into your email settings and check filters, forwarding addresses, and inbox rules. Delete anything unfamiliar. This step is critical because skipping it means the hacker continues receiving copies of your emails even after you’ve changed the password and locked them out.
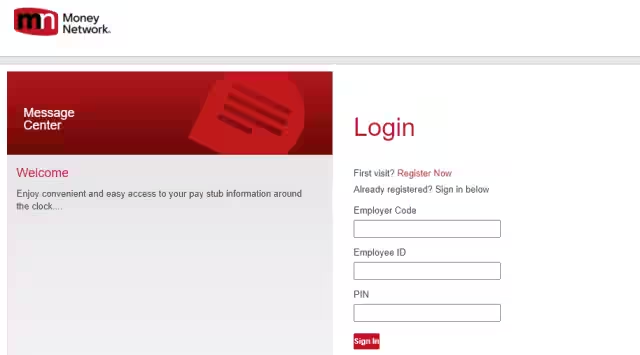
Step 4: Update your recovery information
Check the recovery email address and phone number attached to your account. Make sure they’re yours. Hackers sometimes quietly swap these out so they can trigger their own recovery process later and regain access even after you’ve secured the account.
Step 5: Sign out of all active sessions
Most email providers have a sign out of all devices option in security settings. Use it. Anyone logged into your account from another location gets kicked out the moment you do this.
Step 6: Run a malware scan on every device you use to check email
This step gets skipped constantly, and it’s a mistake. If a keylogger is sitting on your laptop or phone, it will capture your new password the moment you type it. Run a full scan using a reputable antivirus tool, remove anything flagged, and then change your password one more time after the scan is clean.
The Accounts You Need to Check Beyond Your Inbox
An email breach rarely stays contained to just your email. Your inbox is the master key to everything else connected to it.
Check your bank and financial accounts for any transactions you don’t recognise. Look at your social media accounts for posts, messages, or friend requests that weren’t you. Review any account that uses your email address for login or sends you notifications.
Pay close attention to anything connected to payment information. A hacker inside your email for even a few days has enough time to attempt purchases, apply for credit in your name, or drain a connected account before you notice anything is wrong. If you spot anything suspicious in a financial account, contact the institution directly and report it.
How to Make Sure It Doesn’t Happen Again
The fix isn’t complicated. Most email hacks trace back to three things: a weak password, a reused password, or clicking a link that looked genuine but wasn’t.
Use a different password for every account you own. A free password manager like Bitwarden handles this completely. You remember one master password, and it generates and stores everything else. There’s no excuse to reuse passwords once you have a tool that removes the effort entirely.
Be suspicious of any email asking you to click a link and log in, even if it looks exactly like Gmail, your bank, or a service you use daily. Phishing pages are designed to look identical to the real thing. The safe habit is to open a new browser tab and go directly to the site instead of clicking the link in the email.
Keep your phone and laptop operating systems updated. Security patches exist because vulnerabilities are discovered constantly. Running an outdated OS is knowingly leaving a known weakness in place.
Securing a compromised email account, changing passwords, checking connected accounts, and running a malware scan takes about an hour if you work through it calmly. The worst outcomes happen when people either don’t notice for weeks or panic and skip steps.
If you act within the first few hours of noticing something is wrong, the damage is almost always containable.
- How to Tell if Your Email Has Been Hacked (And What to Do Next)? - March 19, 2026
- The Ultimate Guide to Use YouTube Ambient Mode in 2025 - March 17, 2026
- What is MusicLM Research Project and How Does it Work? - March 15, 2026